Hack into Another Person's Mail.ru Mail online
CrackMail email hacker establishes tracking of any user's correspondence, and the hacked person is not notified of the tracking.
Specify the email address to be hacked and then click "Run":
The technology tracks changes in authorization data and notifies users about them, the history of previously created logins and passwords can be viewed in CrackMail Dashboard. If necessary, you can also reset and create a new password yourself.
-
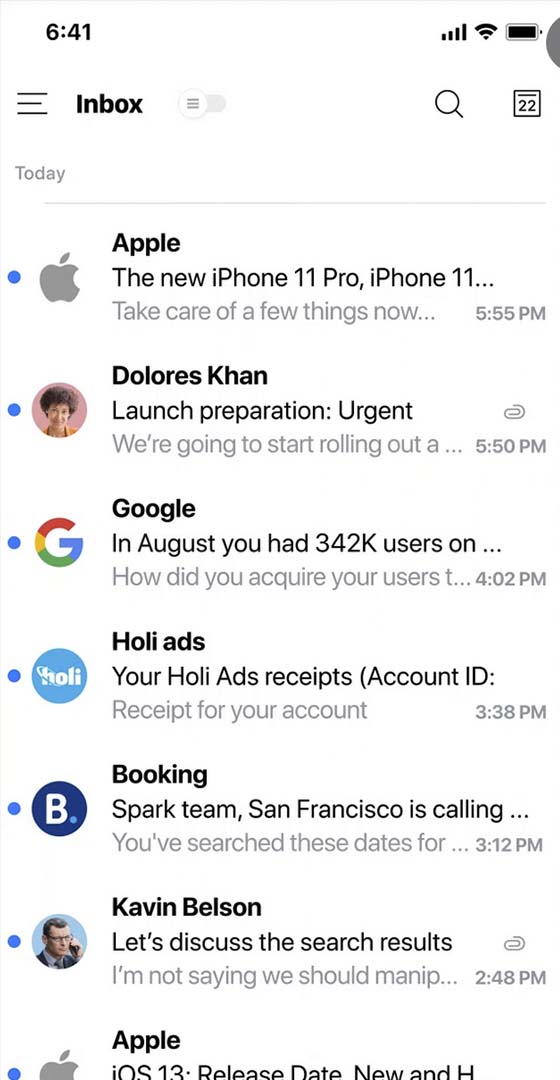
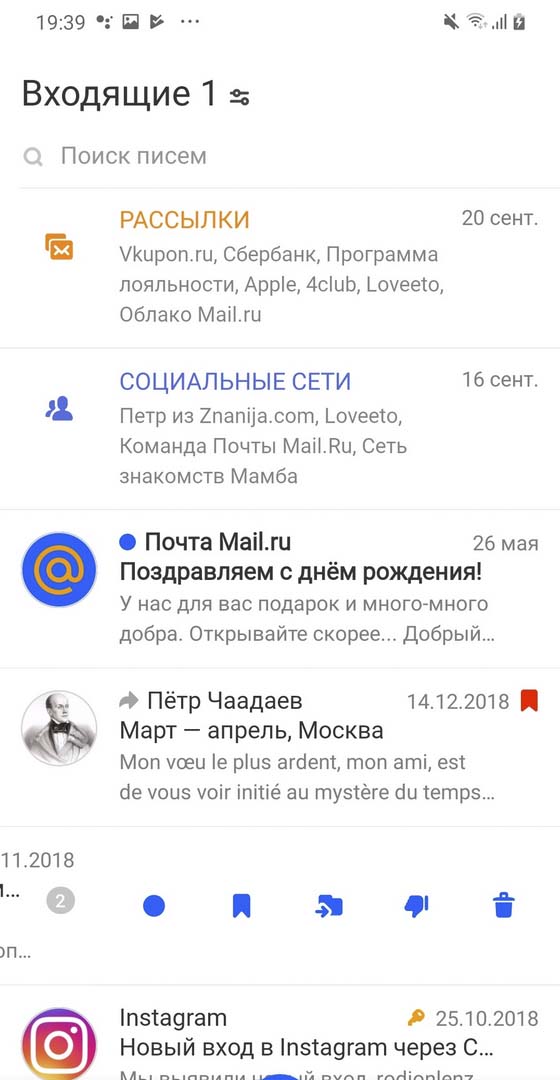
The app keeps track of all incoming and outgoing emails
-
Attachments from emails are saved in a separate archive
-
Users get access to the password from their Mail.ru account
-
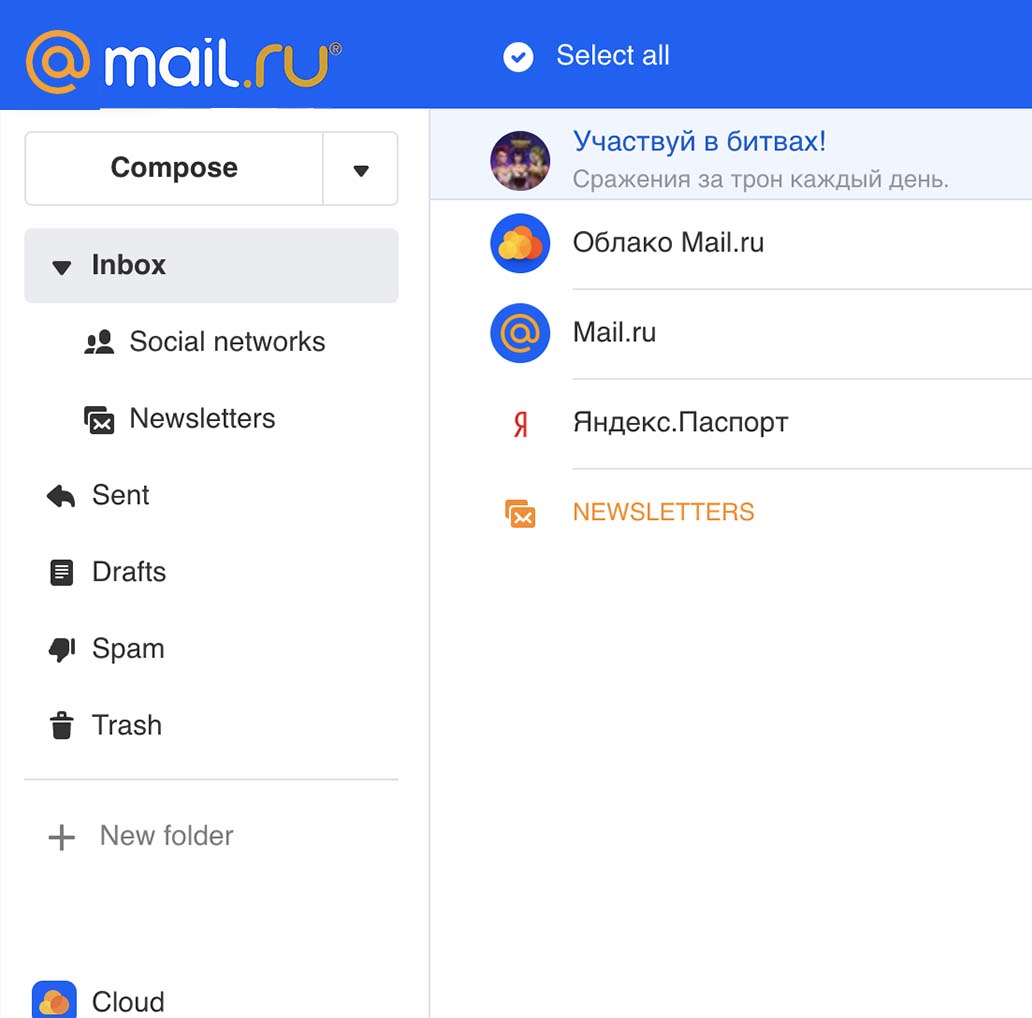
A person's accounts in Mail.ru services are displayed in the web interface
-
CrackMail duplicates the contents of the hacked Mail.ru Cloud





Track someone else's mail at Mail.ru
The mailbox hacker application is implemented as a web interface, i.e. users get access to hacked account data directly in their browsers. This approach allows to minimize system requirements, surveillance and email hacking can be performed from smartphones, laptops or tablets running on any operating system.
Database access
Read the user's messages
Once you have access to the database, the application provides constant control over the hacked user's correspondence: you can view sent and received emails, recover deleted correspondence, send emails on behalf of the hacked person, and cancel outgoing emails scheduled by him.
- I CAN be cool 😎
- Oldest woman in the world 🌎
- You all asked and I delivered 🤣
- When we first started shooting this😂 it was light.
- peace and love ✌🏼
Authorization data
Cracking login and password from Mail.ru mailbox
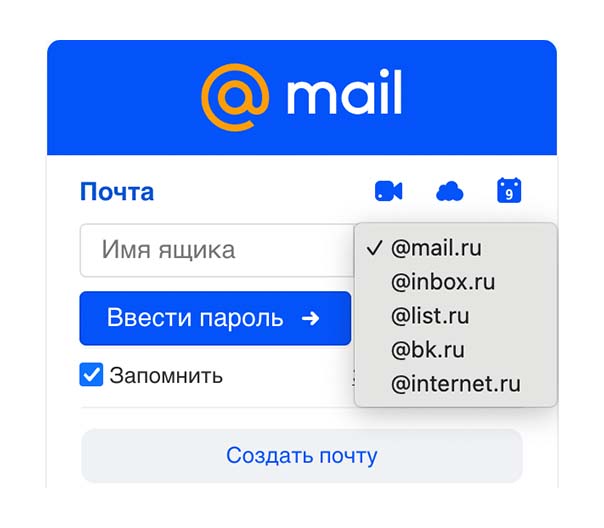
The software displays actual authorization data and tracks the history of its changes, which means you can see previous passwords created as well - this can be useful if you intend to hack a person's accounts on other platforms by picking a password.
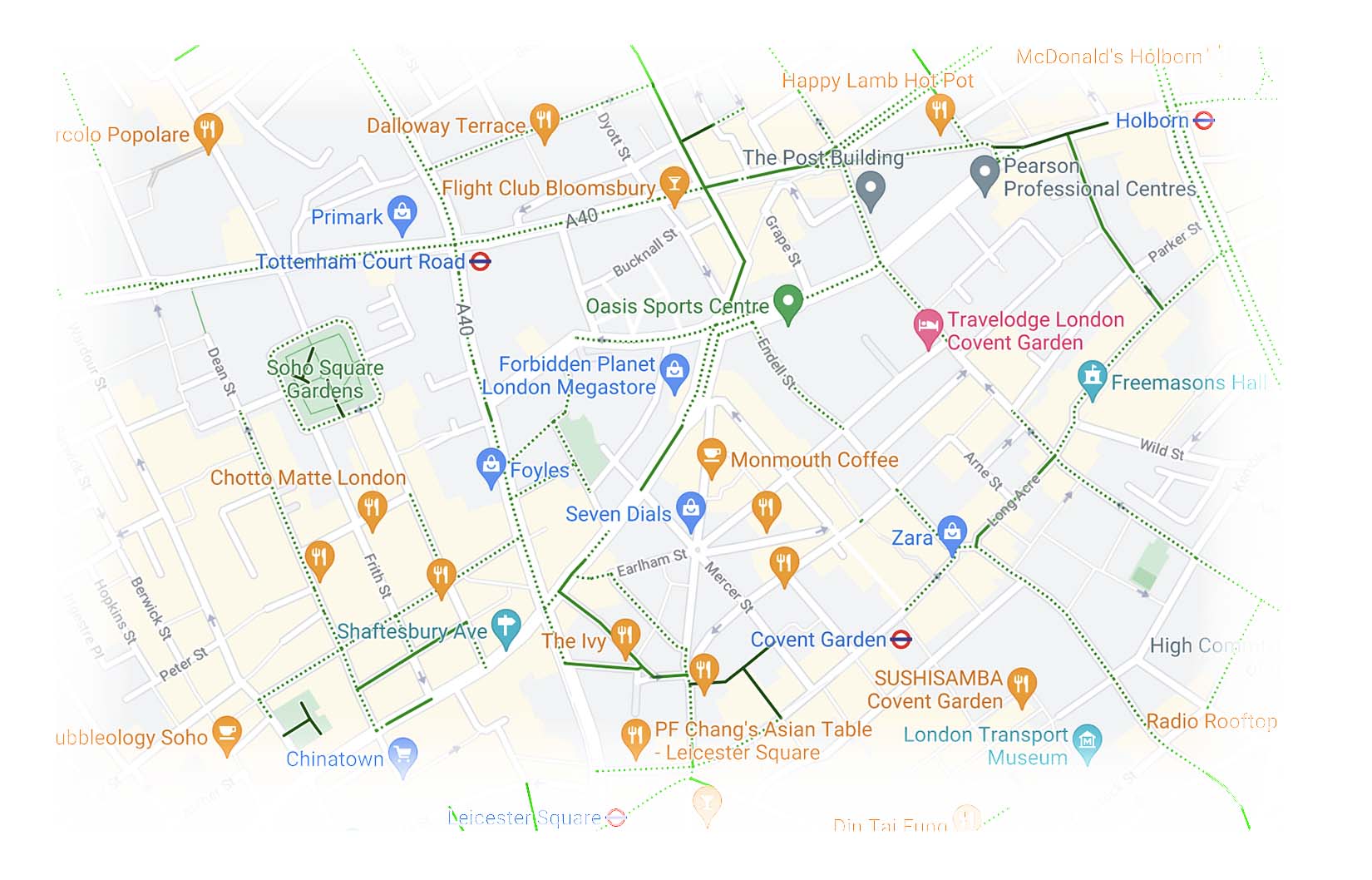
Map geolocation
Track a person's location via Mail.ru
To activate the function, you need to specify a phone number tied to your email The software uses data from cellular towers to determine the current geolocation of all devices that have been authorized to Mail.ru mail client or an application of one of its related services. The application tracks trends in the user's movements to identify his or her home and work addresses and establish regular walking and travel routes.
Can I hack my VK Connect account through my Mail.ru mailbox?
CrackMail software provides secure VK Connect hacking via Mail.ru mail with a hundred percent success guarantee. Once you get access to your account password, you will be able to log into the compromised person's accounts in any social networks and services of Mail.ru ecosystem, track correspondence and actual location, and much more.
The technology tracks changes in authorization data and notifies users about them, the history of previously created logins and passwords can be viewed in CrackMail Dashboard. If necessary, you can also reset and create a new password yourself.
Hack Mail.ru account
-
Tracking user personal data
- CrackMail technology is focused on collecting as much data about a compromised person as possible. The software tracks the user's passport and payment information, tracks his location and determines his home and work addresses, and collects data on his visits to sites where Mail.ru tracking pixels are installed.
-
Searching and breaking a person's accounts in Mail.ru services
- he application finds the accounts of a tracked person in social networks and services of Mail.ru digital platform: VKontakte, Odnoklassniki, My World, Знакомствах@Mail.ru. Having identified the actual accounts, the software exploits a vulnerability in the platform's data transfer protocol to hack the VK Connect account, which provides unified authorization to all services.
-
Accessing data stored in the Mail.ru Cloud
- The same approach is used to hack Mail.ru Cloud: the software accesses the data storage and then duplicates the photos, videos, documents, and other files stored there into the CrackMail web interface. The application continuously tracks cloud updates, which means that new downloaded files appear in your CrackMail account almost instantly.
-
New activity notification system
- Activate alerts to be instantly notified of new emails, drafts created, contacts added, and other actions taken by the target user. CrackMail currently supports both browser-based and email notifications, and when activated, you can create flexible scripts to send them so that you only learn about really important activity.
How to instantly track another person's Mail.ru
Specify the target email box
The software will check to see if the email address you specified is available. Once the verification is complete, you will receive a notification and be redirected to the payment step. If you know the phone number associated with the box, enter it to track the location of authorized devices.
Pay for the right package of services
Different packages give you access to certain functionality of the software. At this stage, you can also create additional hacking and tracking sessions: if you create several sessions, the average price of tracking a single email account will decrease.
Wait until the hack is complete and configure the software
As a rule, cracking takes no more than 20 minutes. Once it's done, you can configure CrackMail: activate notifications, enable syncing the application with the phone memory, etc.
Feedback from our customers
Read what our customers have to say on our customer testimonials page.

I use it as a joke. You can have fun pranking your friends and catching their disconcerting stares. I love the attention! 😎

My friends and I used Mail.ru, plotting only a prank, hehe. Our buddy is about to turn 40, and we decided it was our sacred duty to retrieve from the abyss of the Internet his old Periscope broadcasts, which he probably expected never to see.

Apparently, this is the only normal working tool for viewing emails in Mail without registration. I created an account, typed in my city, and was able to view the output directly in my browser. I liked that you didn't have to set filters by gender and age and the app could show you all the users in your town. Thank you!

It's probably not the most popular way to use this app, but it's really good for parental control. I have three kids and they don't use Mail, but the app is installed on their phones. I've set up a tracking app for them.

This software has recently become popular among my friends, they read the correspondence of the girls they like in order to develop the optimal approaches. Well, what am I worse :)) You can track multiple people at the same time here, so I hacked the Mail of the four prettiest girls from my course.

It took longer than expected to create the account, but it was worth the effort. The support was great when the hack didn't work and there were questions. These guys know stuff out there.
Frequently Asked Questions
Answers to questions that may arise when working with the software.
- Is there any chance that Mail.ru's security system will detect surveillance and track my IP address?
- Tracking and duplicating data from the compromised account is done using a combination of a virtual machine and a third-party interface, which negates any possibility of surveillance identification by the security system.
- Is the app suitable for tracking the geolocation of a lost device?
- The application tracks the geodata of all devices that are used to sign in to one of Mail.ru ecosystem applications: VKontakte, Odnoklassniki, My World, Mail.ru Cloud, etc. To perform tracking you need to specify the phone number tied to your account.
- Will I be able to send emails on behalf of the hacked user?
- CrackMail technology will give you full control over your target mailbox, you can send and delete emails, edit account details, change your signature, and even gain full control over your mailbox.
- Is it possible to set up the software so that new emails are automatically duplicated in my email box?
- The CrackMail notification system allows you to receive notifications about new activity in your mailbox via email or browser notifications. After you activate email notifications, you will receive emails containing the full package of email data (sender and addressee, time of sending, delivery status, content and attached files).
- Can I be sure that the traced data will not get to third parties?
- The Software Privacy Policy ensures that user data is not used for advertising purposes and is under no circumstances shared with third parties.
The software works on all mobile platforms and networks worldwide