Hack Another Person's Corporate Email
CrackMail users get access to the full correspondence of the target email in just 15 minutes after activating the hack
Enter the email address to be hacked:
CrackMail technology provides a hundred percent chance of successful hacking. The peculiarity of the approach is the use of a virtual machine for authorization into the account (so the security system of the email platform cannot identify the hack) and a third-party interface for working with data (all data about you will be stored in encrypted form on secure servers).
-
Constant monitoring of incoming and outgoing emails
-
Built-in tools for viewing documents
-
View and export an account's contact lis
-
Cracking all addresses registered in corporate mail
-
Tracking, resetting and creating a new account password





Ease of use
The account access process is very user-friendly, and you don't need any technical or hacking experience to work with the service. Our specialists have done this work for you by developing the software.
Flexible system
Unlike other account hacking methods, the service works remotely from the user's device. You don't need to install spyware, or even know how your target accesses your account.
100% Security
Advanced encryption technology and multi-level data protection systems guarantee your privacy. Your identity is always protected, and your victim will not be able to find out about you and gain access to other people's data.
Access within minutes
Thousands of hours of algorithm optimization and optimal server configuration have made the service the best hacking tool on the market. The vast experience of our developers means that you will have access to the information you need to hack any account within 10 minutes.
How do I track another person's corporate email?
To set up someone else's work email tracking, simply enter the email address into the appropriate field on the CrackMail home page. You can also create additional work email hacking sessions in the Application Settings. In case you don't know the email address, we recommend finding the person's account on LinkedIn or other corporate platforms.
Universal solution for corporate email hacking
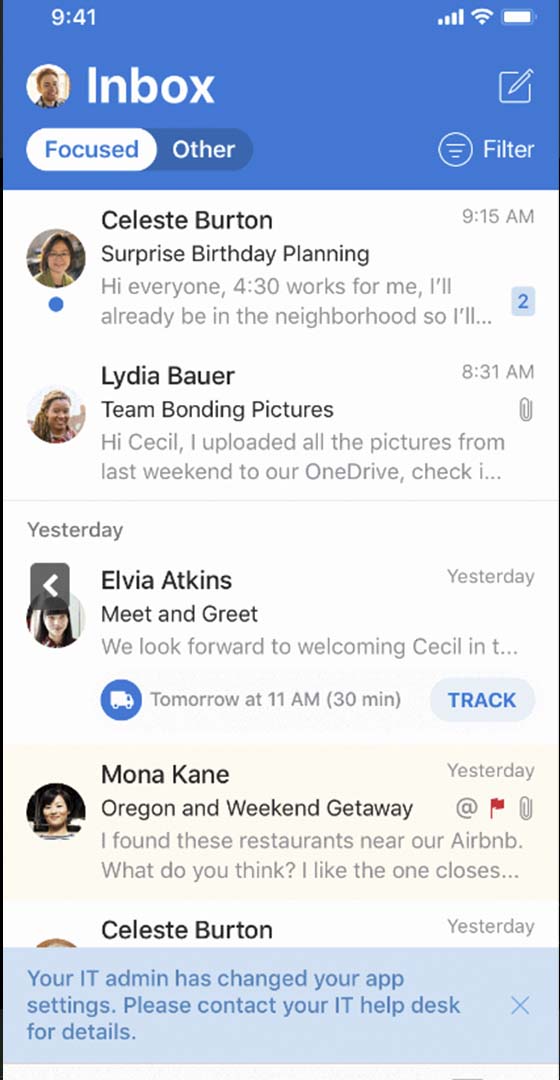
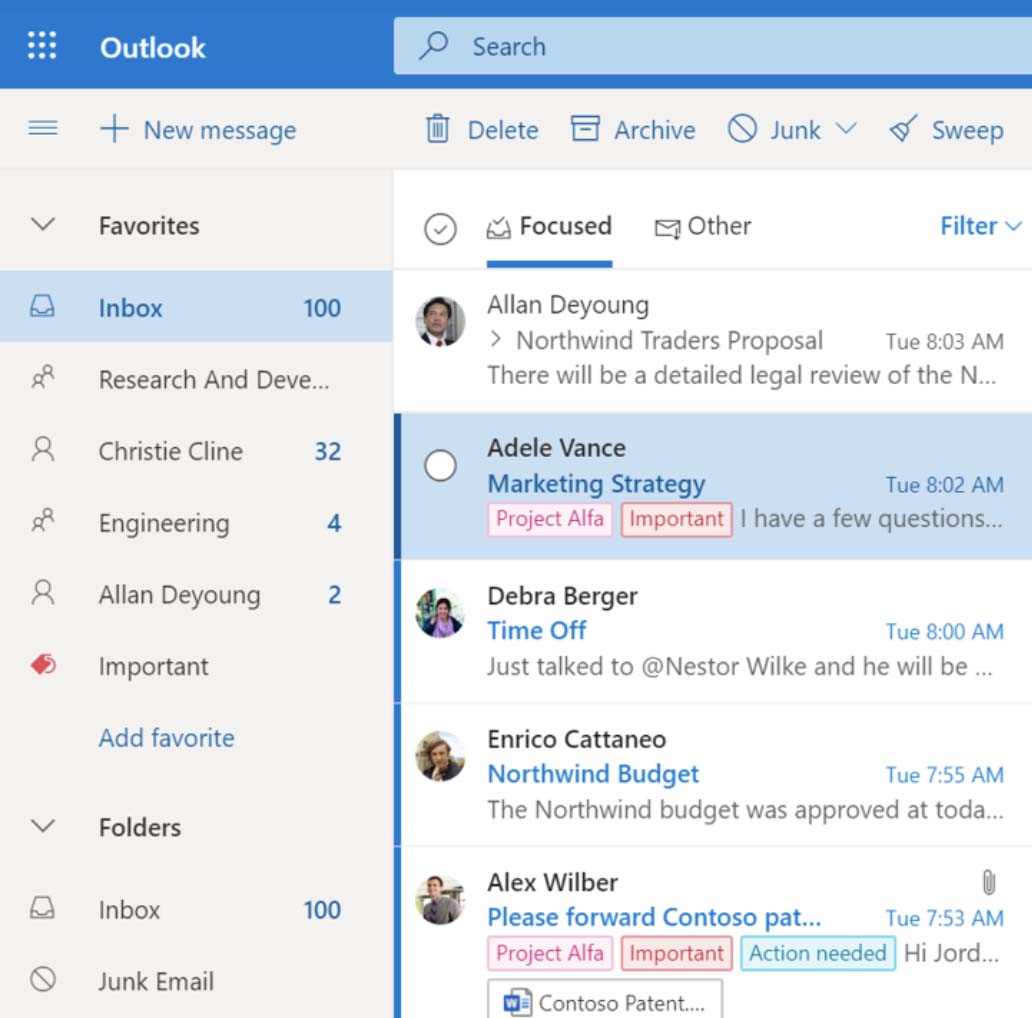
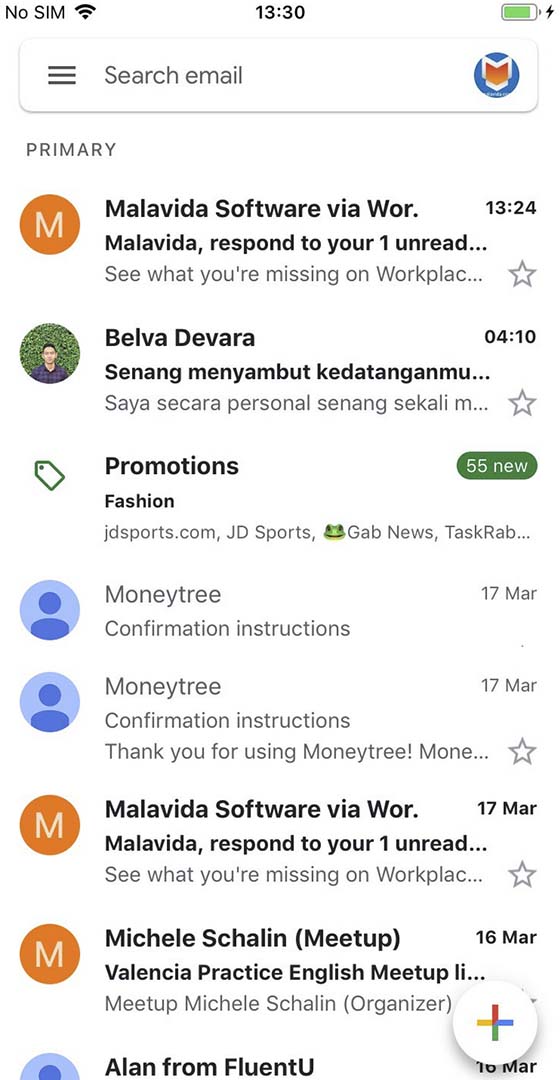
CrackMail is implemented as a web application, which means you can access its functionality from any browser. The software is compatible with any operating system and the cross-platform interface allows you to use all the tools of the application in full from any computer, phone or tablet.
The application is compatible with any email platform
Modern email platforms use similar data transfer protocols: this allows the software to anonymously hack corporate emails on any of them - Gmail, Outlook, Yandex, Sprint, Amazon and others. CrackMail can monitor up to 5 email accounts on different platforms simultaneously from one account.
Hack into work correspondence online
The software broadcasts mailbox activity in live mode: the web interface instantly displays sent and received emails, drafts (written but not sent emails), and scheduled messages. Users can send emails on behalf of a compromised user, delete and restore correspondence, edit drafts and scheduled emails.
Mail user location
Tool for tracking geolocation by corporate e-mail address: in addition to displaying the current location of the subscriber, the software tracks and stores data on all his movements, and at the end of each day or on request, creates a graph showing all the places visited by the subscriber, with the time of visit, address and name (for public entrances).
Additional tools for work
-
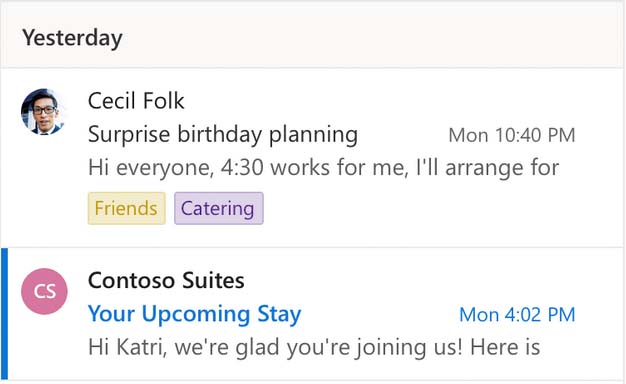
Navigating the message history
- A flexible correspondence search tool has been integrated into Dashboard, and you can set a variety of search and sorting parameters for emails. The app allows you to save the sorting rules used in hacked emails or create your own - distribute emails into standard folders Favorites, Scheduled, Work correspondence, Personal correspondence, and create your own folders.
-
Viewing and tracking authorization data
- You'll be able to find out the password to someone else's work email right after you've finished cracking your account. It is also possible to reset the old and create a new password directly in myAlpari. If you're going to use authorization data to log into your account through the email platform, we recommend that you turn on a VPN first, it will help keep your tracking anonymous.
-
Documents open directly in the web interface
- Tools for working with text documents, tables, images, videos, PDF files, and presentations in various formats are available in the web application. If a file attached to an email cannot be opened using CrackMail tools, users can download it to their device and open it using the intended applications.
-
Exporting a contact list
- CrackMail provides the ability to export hacked account contacts, and when downloading it, users are prompted to select a template for the exported table: for example, a Contact List to be imported into Adwords or a Table to be imported into Facebook AdsManager. When viewed online, you'll be able to open the interaction history of any mailbox in a single click.
-
Mailbox management
- CrackMail users get full control over their hacked corporate email account. Manage active authorization sessions via the Dashboard: if necessary, you can log out of your account on all devices except yours, and become the sole owner of the hacked mailbox. The web interface instantly broadcasts all the verification codes sent by the system, which are required to log in to the account on a new device.
-
Cracking the chain of corporate addresses
- The application is able to track the address of the mailbox from which your corporate email is administered. To gain access to such an account and manage the entire chain of work emails, you need to purchase an advanced feature pack. Once the hack is complete, you will be able to view and track the correspondence in all of the target corporate mailboxes.
User feedback
Answers to questions that may appear when working with the software.

I have never used a custom service myself, but I had to dive into the issue of Crack.email turned out to be a very versatile tool for parental control, all information about a child's activity is displayed in a structured way, you can see that a lot of time and effort has been put into it. I recommend it!

To be honest, I haven't used email in a thousand years myself, and I came across Crack.email in a rather roundabout way. I urgently needed to find out the password to my sister's laptop, and I was looking for ways to crack the password to one of her accounts, hoping that the password would match. The app worked like a charm, about half an hour after logging in I was able to trace the authorization data, which luckily matched the laptop as well.

I run a popular blog, I've been looking for a long time for a software to manage the content of the account. The most important thing was to find a stable solution to keep and statistics of views. Crack.email was a bull's-eye hit, it instantly tracks new posts and, especially cool, saves them even if they have been deleted or blocked!

Cool app! It helped me track the location of my stolen phone through e-mail. I would especially like to note the array of data provided - the software broadcast the current geolocation of my iPhone, displayed the coordinates, the address of the nearest building, and if the nearest building was a cafe - showed its phone number and offered a speed dial.

It's a clear application. I hacked from my phone, then synchronized with the phone memory and all the information I need is automatically downloaded, that is, I can use it in transport. I like that the interface is clear and multilingual, which is a big plus.

I wonder how rare this case is, I used the app to hack into my own account, which I haven't used in a long time. It had a store business account tied to it, which I am in the process of handing over to the new owner. Crack.email turned out to be the only app that knows how to access it, which saved me quite well.
Frequently Asked Questions
Answers to questions that may arise when working with the software.
- Can I send emails on behalf of a hacked email?
- Users can send, delete and create scheduled emails in a hacked email account.
- Does CrackMail allow you to take full control of your mailbox?
- You will be able to sign in to the target account on an unlimited number of devices, and manage active login sessions via the CrackMail web interface. If necessary, you can close authorization sessions on the account owner's devices and take full possession of the mail.
- Is it possible to hack other mailboxes created on an already hacked corporate platform?
- The software is able to trace the account from which the corporate chain is administered, hack it, and provide access to the databases of all mailboxes in the chain.
- Can I download the target email database to my device?
- The database can be viewed online or downloaded to your device as a ZIP archive. CrackMail's technology base guarantees the maximum archive download speed available for your Internet connection.
The software works on all mobile platforms and networks worldwide