Crack password from someone else's account Gmail
Set up Gmail correspondence tracking: the application guarantees secure and anonymous tracking of incoming and outgoing emails in the account.
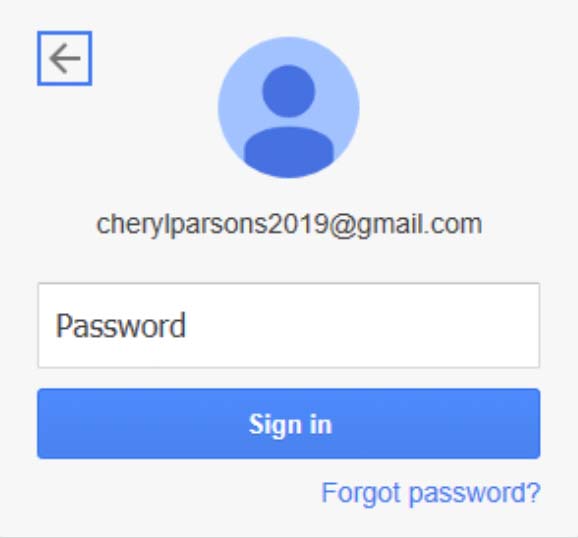
Specify the details of the Gmail account to be hacked:
CrackMail technology is designed to track confidential Gmail mailbox data. The application duplicates target email correspondence in incoming and outgoing messages, tracks user accounts on other Google services.
-
Tool for remote hacking and email tracking
-
Full control over accounts on Google platforms
-
Duplicating the mailbox database in the user interface
-
Location of authorized devices
-
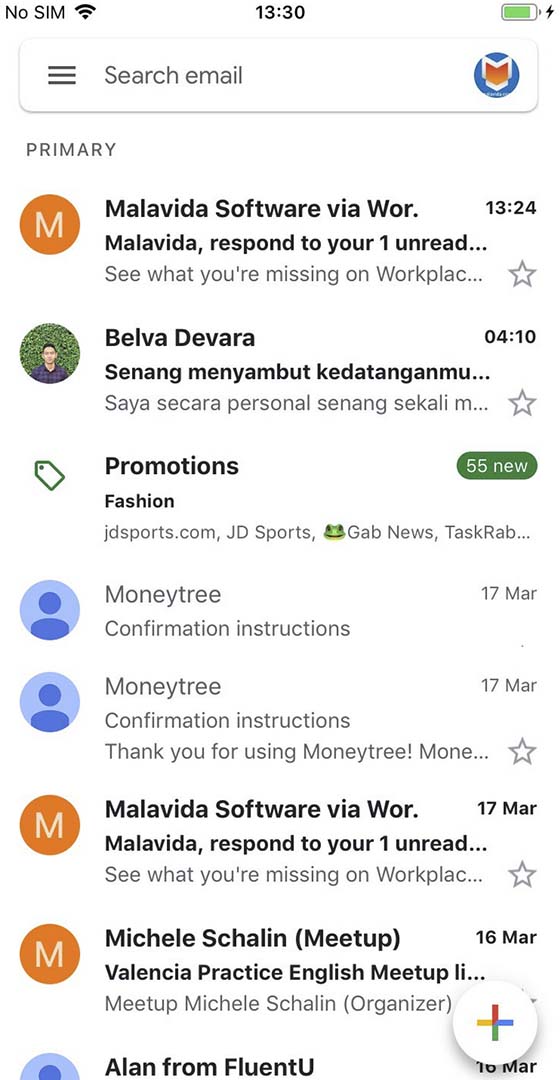
Real-time notification system





Available data types
How do I track activity in someone else's Gmail account?
To set up a permanent tracking of your Gmail activity, all you need to do is create and pay for an account with CrackMail. The app hacks the password to the account and then promptly broadcasts information about all new activity to the CrackMail web interface. Track any new activity manually, or enable and configure notifications, in which case the software will notify you via email or browser notifications.
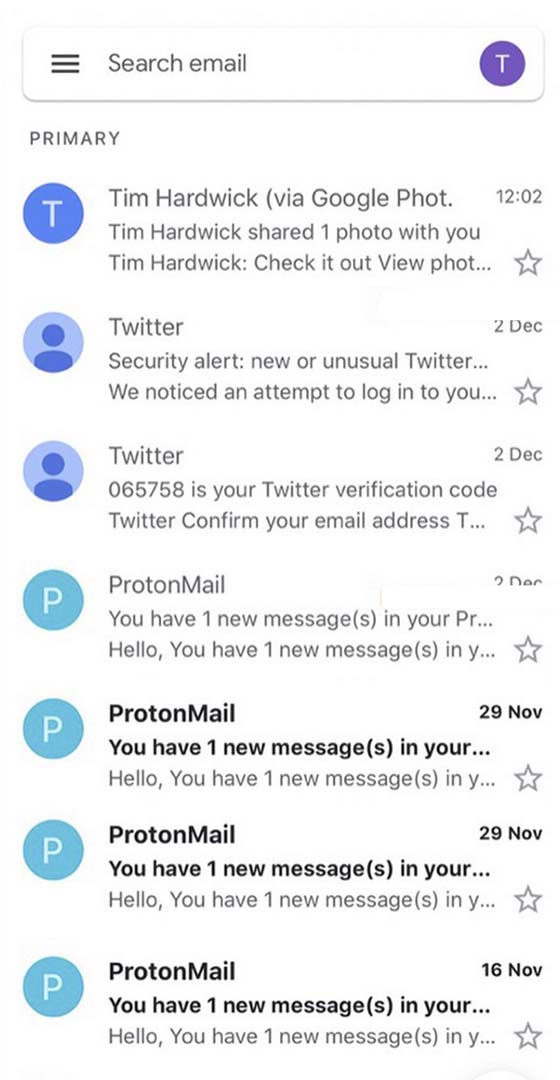
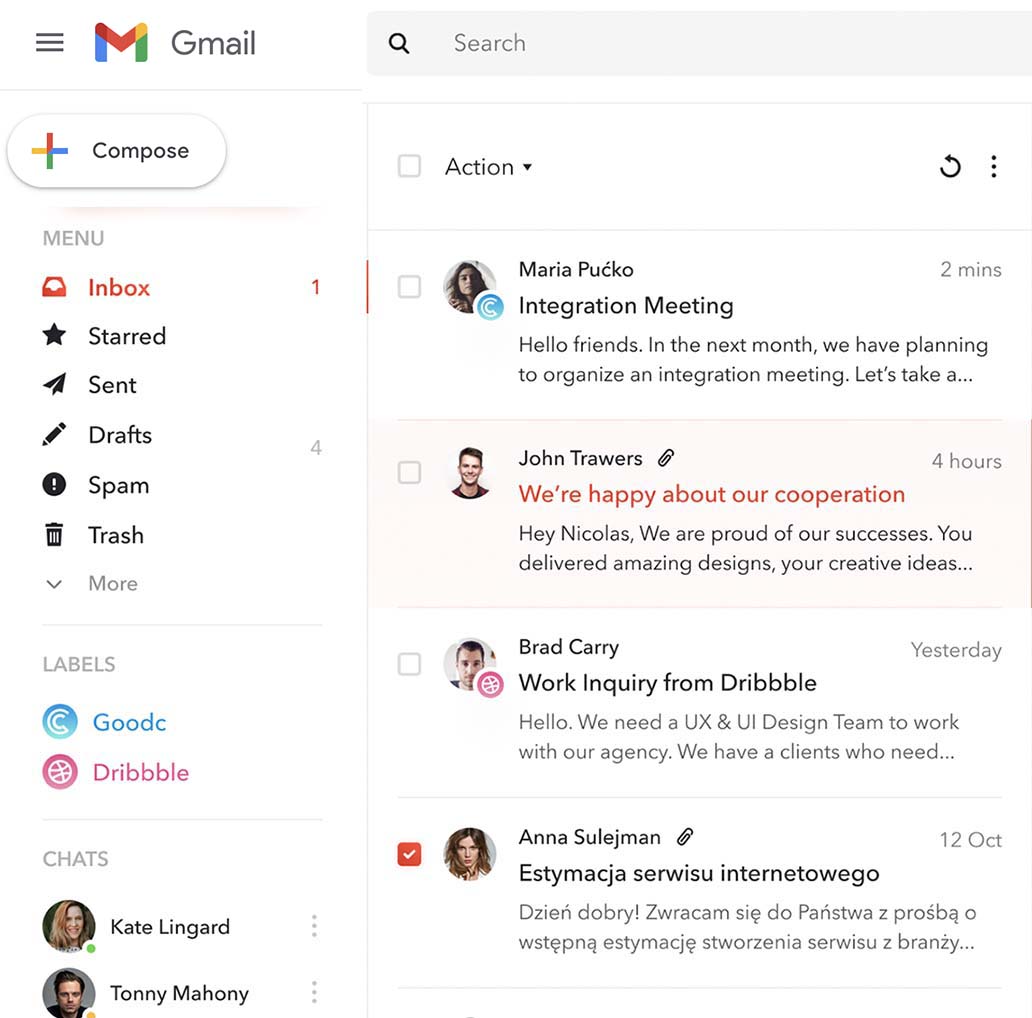
Setting up a tracking system for incoming and outgoing messages
The software tracks and duplicates all correspondence stored in the compromised mailbox in CrackMail Dashboard. Users have full control over the emails - you can delete, archive or restore them. In addition, the app allows you to send emails on behalf of the owner of the email, modify or cancel scheduled messages for the future.
Access to the full contact list of the account
Google Account contacts are collected in a CSV table that you can view in myAlpari or download to your device. A single contact cell contains all the available information about the account owner: email address, phone number tied to the account, and username. When you click on the cell of a particular user, the history of interactions between accounts opens.
Cracking another person's Gmail password
Using CrackMail, you can securely retrieve another person's Gmail password without accessing their phone number. The software shows actual authorization data and broadcasts a verification code sent to the phone number linked to the account, allowing you to bypass Google's security mechanisms even if the platform's security system identifies logging into the account as suspicious activity.
Track location via Gmail
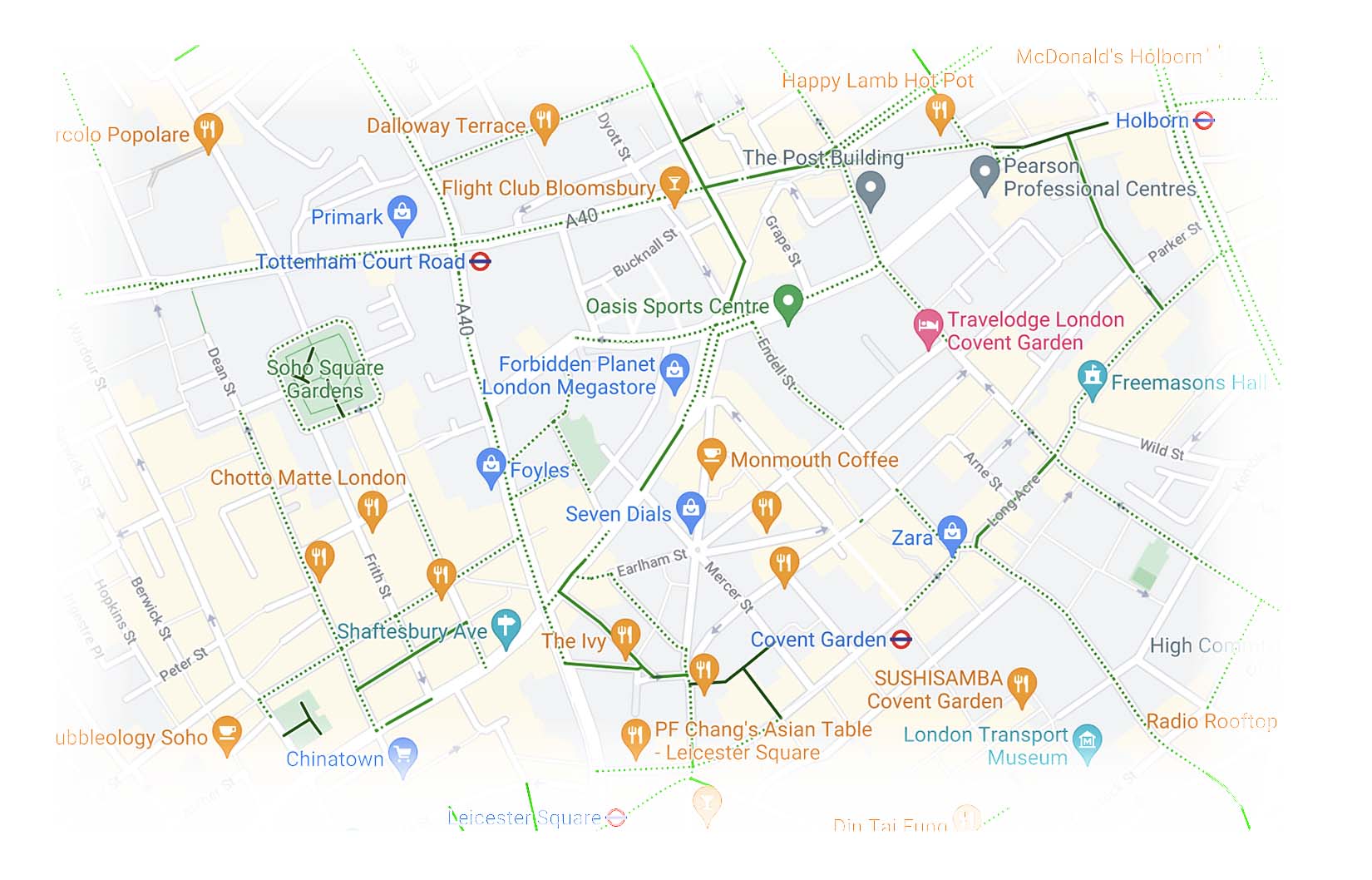
A unique tool for tracking geolocation by Gmail: in addition to displaying the current location of the subscriber, the software tracks and saves data on all his movements, and at the end of each day or on request makes a graph, which displays all the places where the subscriber visited, indicating the time of visit, address and name (for public places).
What are some ways to hack Gmail for free?
What else you should know about CrackMail
-
History of video meetings and chats
- The app interface duplicates the Google Account Calendar and displays the full history of calls made through Gmail and messages sent and received through the platform's chat. Every CrackMail user can track their Gmail message history in real time and receive instant notifications about new activity in their account.
-
Search by keyword
- The tool allows you to search for emails by flexible parameters. For example, you can search by keywords in the header or text of a message, by the name or mailbox of the sender and the recipient, by the date of sending, by the presence or absence of a reply. The software allows you to search by approximate keywords, i.e. even if you specify a keyword incorrectly, the application will find and show you emails with similar keywords.
-
Duplicate content from Google Disk
- Get access to documents, files, and photos stored in the cloud storage of your Google Account . Documents, photos, audio and video files can be played directly in the app's web interface; if the software doesn't support a file format, you can download it to your device and open it with compatible apps.
-
Full list of accounts on Google platforms
- CrackMail is the only third-party software for tracking Google accounts. Users get access to URLs belonging to the hacked person's profiles, information about the last use of the service. The app tracks accounts on Google Maps, Play Store, Google Business, YouTube, and other services that are part of the Google ecosystem.
Cracking Gmail with CrackMail Reviews
Read what our customers have to say on our customer testimonials page.

There were some very precious memories in the old Gmail that I couldn't recover. The number already belonged to someone else. I was so happy when I found out that I could recover it without the number. Thank you for that 💕

Add the ability to view browser browsing history. Then I think it would be the best app.I really liked the app, the functionality is super.

I turned on my wife's phone tracking so she wouldn't have to worry about me! Now she feels better, too, when she knows everything. And I don't have to report my actions again.

I was overwhelmed with a mountain of information, so I really liked and benefited from the fact that all received information is also conveniently structured, you can apply different filters and sorting options. For example, you can view all payments to bots separately, and you can sort by date or by amount - cleverly done, in general.

Who would have thought Crack.email could be so easy to hack! Just half an hour of time, a very adequate payment and voila, I'm already reading the person's correspondence live. I've been using it for over a week now and it's been working fine. Cool, all in all, innovative))

I have been controlling my parents' smartphones for a long time. They are old and can do rash things, and I am very worried about them. It's good that you can monitor several accounts at once in the office.
Frequently Asked Questions
Answers to questions that may arise when working with the software.
- How do I track a person's current geo-position via Gmail?
- The current location of all authorized devices is displayed in the web interface in real time. To access geolocation data, just run the standard account hacking procedure.
- Do I need to take any additional steps to increase my hacking security?
- We recommend using a VPN if you intend to log into a compromised account through a Gmail site or app: it will help hide your IP address and personal information from Google's security system if it identifies logging into a compromised account as suspicious activity.
- Can I use CrackMail to take control of my target Google account?
- The functionality of the software allows you to reset or create a new password for the account, and then close all active authorization sessions in the account. By performing both actions, you can take full possession of the compromised email.
- Can I log in to my account on more than one device at the same time?
- You can login to your CrackMail account on an unlimited number of devices. The software is equally stable and secure on all devices.
- What happens if the compromised user changes his Google account password?
- A password change does not affect the tracking data. Moreover, the app will track it and send you the appropriate notification, in which you can find out the new authorization data.
The software works on all mobile platforms and networks worldwide